What Is the Financial Impact of a Ransomware Attack?
The reason for ransomware’s popularity boils down to one thing: economics. Without the proper defenses, cybercriminals can extort hundreds - sometimes thousands - of dollars from SMBs by encrypting valuable data and demanding a ransom be paid to restore the data. Below, see the rise in the average ransom amount by year (in US dollars):
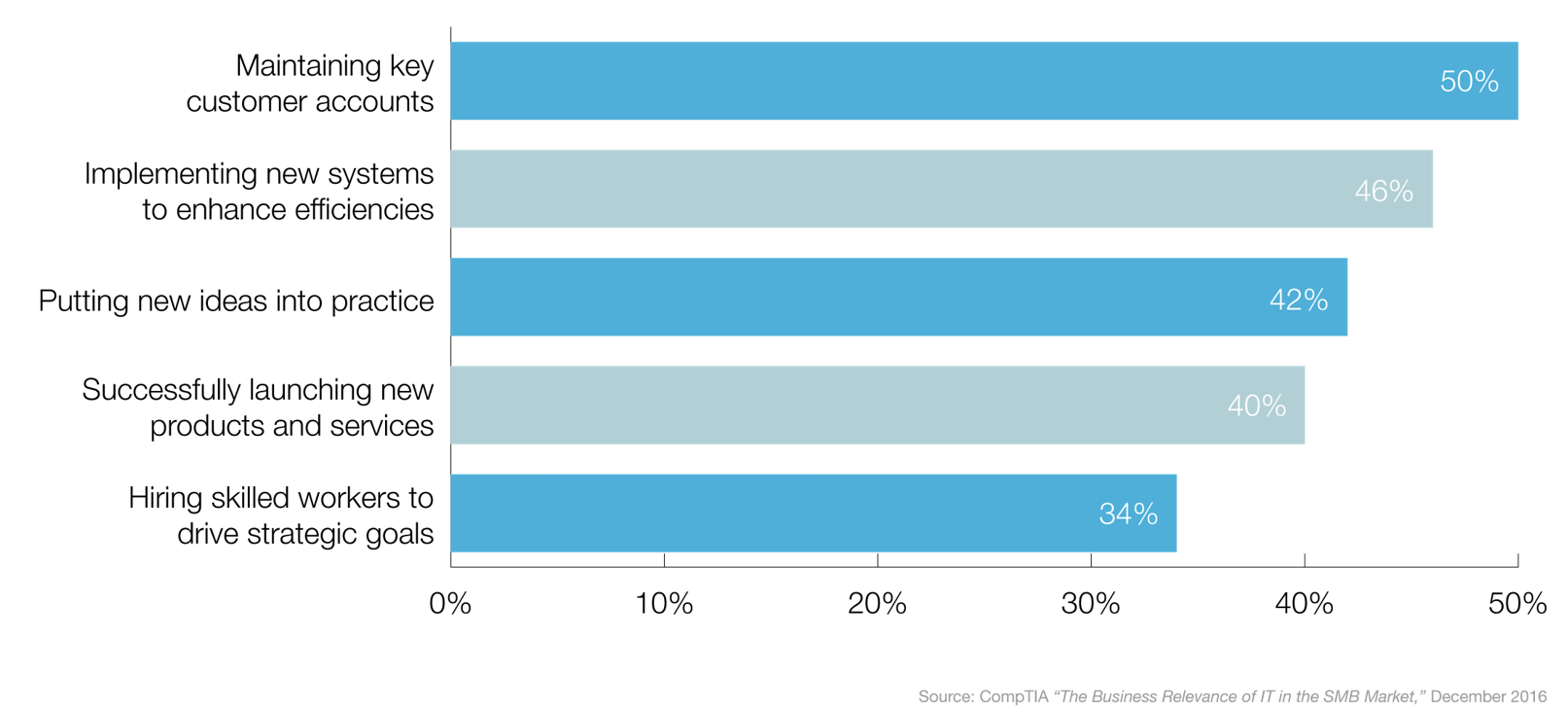
How Managed IT Services Align with SMB Business Priorities
Despite the need to embrace technology and IT innovation, most SMBs lack the necessary vision, strategy and resources. However, partnering with a managed services provider can help SMBs address these challenges to achieve strategic growth that aligns with their business priorities’ - including the top SMB business priorities that are depicted below.
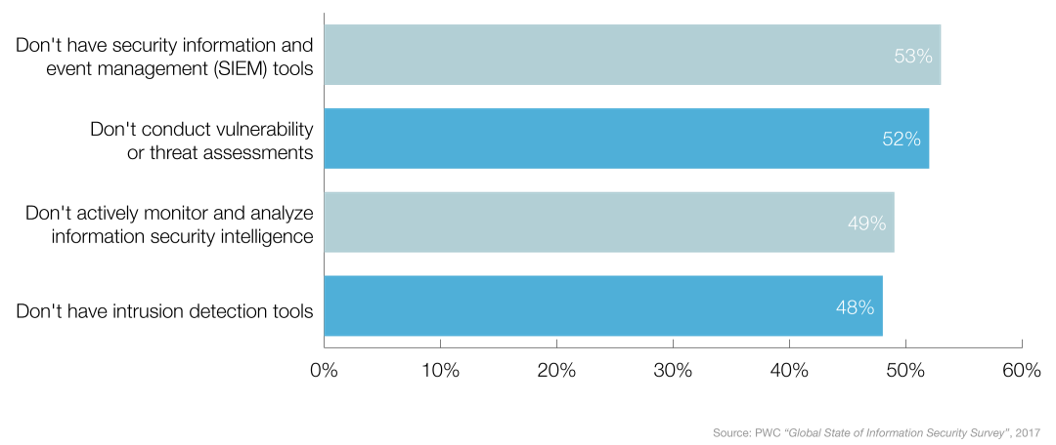
Information Security: SMBs Need It, MSPs Can Provide It
Due to the quickly evolving cybersecurity landscape, many SMBs lack the ability to keep up and are ill-prepared for the threats that exist today. Below are the percentage of organizations that don’t have the following threat detection tools and processes in place.
Should You Beware of Ransomware?
Today’s ransomware landscape has grown exponentially over the past two years and continues to rise. Without proper protection and defenses, SMBs are vulnerable to the increased volume of threats to their IT systems. Below are the annual number of discovered ransomware families, including the projection for 2018.
Is the IT Security Gap a Threat to SMBs?
With lean IT staffs, many small- and medium-sized businesses (SMBs) lack the resources and expertise to manage complex security infrastructures. While threats to security are proliferating, these organizations aren’t taking the proper precautions to protect themselves and their networks. The data below shows the gap between the level of concern and the level of protection for given IT security issues.
Is Your IT Security Strategy Incomplete?
Security is a major concern for many small- and medium-sized businesses (SMBs), yet many of them do not have the proper plans in place to respond to and recover from a disaster situation or security incident, which can leave them vulnerable to costly downtime and data loss. Below are the percentage of SMBs to which the following applies:
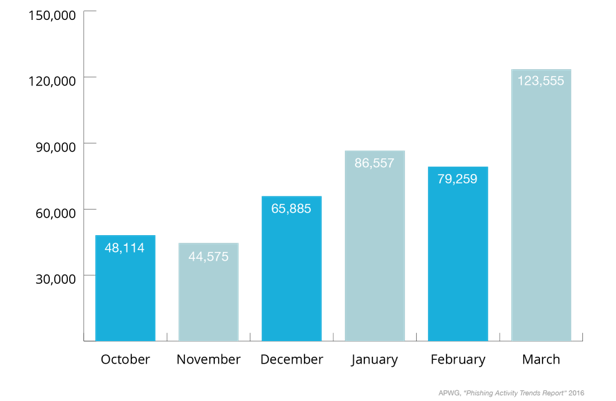
Are Cybercriminals Phishing for Your Sensitive Business Information?
With phishing attacks steadily on the rise, businesses have to be especially careful when clicking links or opening email messages from untrusted sources. The chart below shows the number of unique phishing websites detected monthly, from the last quarter of 2015 through the first quarter of 2016.
Are Outdated Browsers Leaving Businesses Vulnerable?
Running unpatched browsers leaves your network vulnerable to exploits and other malicious schemes that could expose or compromise company data. The chart below breaks down commonly-used browsers by the percentage of users running outdated versions of each.
3 Child Safety Apps to Download for Halloween
1. Location Apps
There are some great apps out there where you can track the movement and location of a wireless device. Most mobile carriers – definitely Verizon and AT&T – have their own family locator app, which is usually available with a monthly charge. Most of these apps will typically run incognito so that the person using the phone doesn’t know their location is being tracked. This is a perfect option if you want to give your kid a sense of independence while also keeping tabs on their safety. One highly-rated, free location app called Follow You, Follow Me allows users to track and view each other’s location, and is available for download from the Apple iTunes store. Similarly, GPS Phone Tracker can be used to find a user’s phone and track their whereabouts at any given time, and is available for download from the Google Play Store. If you really want to take the extra step here, consider installing a panic button app that can be used whenever you or your loved one is in trouble.
2. Set or Automate Check-In Times
You can set an alarm using the pre-installed alarm app on your child’s mobile device to alert them when it’s time to check-in with you. If you’re worried that they’ll just hit the snooze button, you can use apps like SchedCall (Android) and CallBot (Apple) to automate calls to a designated phone number. Some of these apps allow you to schedule calls to multiple people at the same time, while others work their way down a hierarchy of people if the call is missed. The app can alert any parent or guardian first, and if they’re busy, you can arrange for another close friend or relative to be next in line.
3. ICE and Education
Most of us neglect the ICE (In Case of Emergency) contact lists in our phones, or don’t even know how to add an ICE contact in the first place. In the event of a true emergency, having an ICE contact can help emergency personnel find the right person to immediately get in touch with. These numbers should be one of the FIRST places they check to notify you or another close relative. Most phones have this feature built in, but yes, there are apps for that. For easy access and visibility, most apps allow you to place a widget on the home screen of the device, or you can always ask Siri to help out.
Lastly, these tips and tools are no good if your child doesn’t know why they’re important and how to use them. Most kids seem to have smartphone skills ingrained in their DNA nowadays, so it shouldn’t be an issue to educate them. Furthermore, you can reinforce this education in your local community. If you’re a member of a neighborhood watch or a similar group, spread the knowledge and share these tools with them.
Email: mail@simplesky.net
Phone: 319-252-1122